Supply Chain Attack:The Hidden Systemic Threat Behind Modern Digital Ecosystems
Supply Chain Attack
Lately, I’ve been thinking a lot about how cyber threats are evolving, and one pattern that keeps standing out is supply chain attacks. They’ve quietly become one of the most effective ways for attackers to get in. Instead of breaking through a system directly, they take advantage of how everything is connected today—software distribution, cloud services, and even third-party dependencies.
What’s interesting is that attackers don’t always need to exploit a vulnerability in the traditional sense. They can simply ride along trusted integrations to gain initial access. A study back in 2022, “Supply Chain Characteristics as Predictors of Cyber Risk,” actually highlighted this pretty well—basically showing that the more complex our digital ecosystem becomes, the higher the probability of cyber incidents.
 Full screen width and center alignment
Full screen width and center alignment
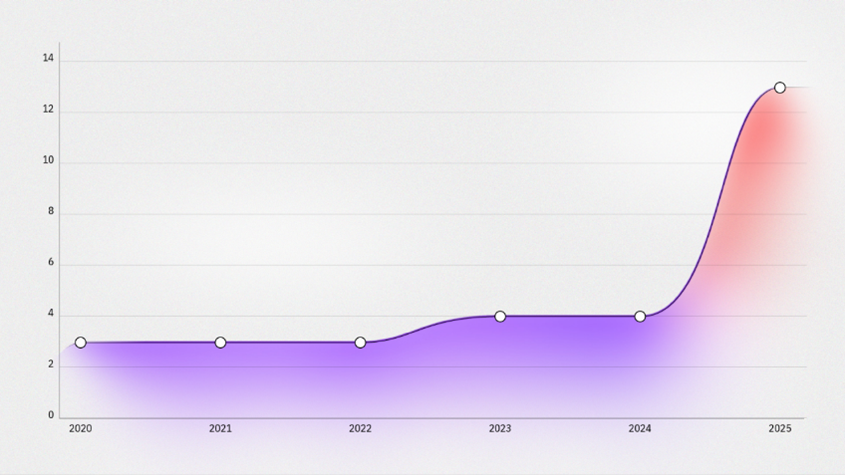
And if you look at recent data, it really backs this up. The IBM X-Force Threat Intelligence Index 2026 reported that supply chain compromises have increased almost fourfold over the past five years. That’s a huge jump. It shows a clear shift in attacker strategy—moving toward abusing trust instead of just exploiting weaknesses.
 Full screen width and center alignment
Full screen width and center alignment
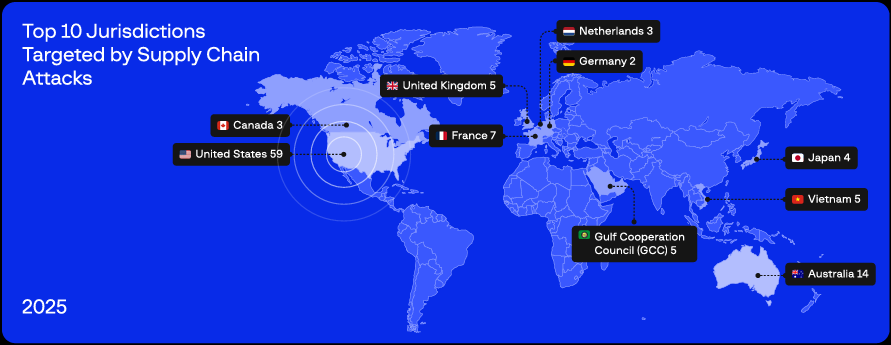
What makes it even more concerning is that this approach allows attacks to scale. Once attackers gain access through a trusted component, they can potentially impact multiple organizations within the same distribution chain. Reports like the High Tech Crime Trends Report 2026 from Group-IB also point out that both state linked groups and cybercriminals like Lazarus, Scattered Spider, HAFNIUM, DragonForce, and others—are actively leveraging this technique.
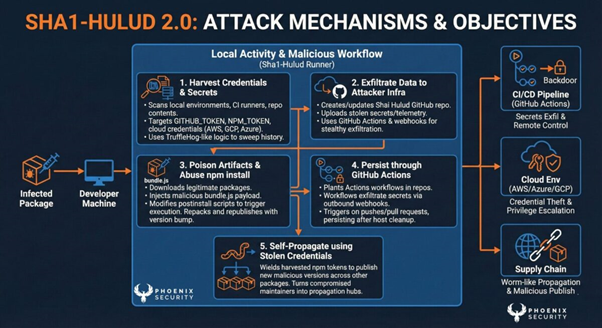
One case that really caught my attention was a campaign in the NPM ecosystem linked to something called Shai-Hulud. In this scenario, attackers injected malicious code into packages or published modified versions. When developers installed those packages, the malicious code would automatically run, stealing credentials like GitHub tokens, NPM credentials, and even cloud access keys. From there, those stolen credentials were used to compromise more packages, allowing the attack to spread further across the ecosystem.
 Full screen width and center alignment
Full screen width and center alignment
What makes supply chain attacks particularly tricky is how well they blend in. The malicious activity often looks just like normal system behavior. In logs and monitoring tools, everything can appear legitimate, which means many traditional security controls struggle to detect anything suspicious in the early stages. This gives attackers plenty of time to maintain access, move laterally, and expand their control without being noticed.
And the impact goes beyond just technical damage. We’re talking about real consequences—operational disruption, financial loss, and reputational damage. That’s why I think supply chain risk shouldn’t just be seen as a technical issue, but as a strategic one that needs attention at the management level.
At the end of the day, organizations need to shift their approach. It’s no longer enough to just protect the perimeter. We need better visibility into how systems integrate and how software flows across the environment. Adopting a Zero Trust mindset becomes essential where nothing is automatically trusted, and every process needs to be verified before being considered safe.
Reference :
- https://arxiv.org/abs/2210.15785
- https://www.ibm.com/reports/threat-intelligence
- https://www.ibm.com/think/insights/more-2026-cyberthreat-trends
- https://www.enisa.europa.eu/publications/threat-landscape-for-supply-chain-attacks
- https://www.group-ib.com/media-center/press-releases/htct-2026-supply-chain/
- https://jfrog.com/blog/shai-hulud-npm-supply-chain-attack-new-compromised-packages-detected/
- https://phoenix.security/shai-hulud-campaign-timeline/